Monday, March 28, 2022
Trusted CI Publishes 2022 Report Summarizing its Impact on Over 500 NSF Projects
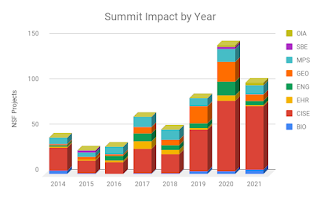
We define "impact" as the number of NSF projects (awards) that have had an engagement with Trusted CI or have had staff attend a Trusted CI event; including the NSF Cybersecurity Summit, webinars, and training events. Using that metric, we find that since 2012, Trusted CI has interacted with over 500 NSF projects, including over 300 NSF projects during the last 3 years (2019-2021).
The full report includes more details about our impact broken down by NSF Directorate, our engagements, Summit attendance, and more. It is available at https://doi.org/10.5281/zenodo.6350540.
Tuesday, March 22, 2022
White House Fact Sheet on cybersecurity protections
On March 21, the White House published “FACT SHEET: Act Now to Protect Against Potential Cyberattacks” providing guidance on protection against potential Russian cyberattacks in response to sanctions. The White House post was covered by CNN, NBC News, Reuters, Bloomberg, and others.
The guidance in the Fact Sheet, specifically the Cybersecurity & infrastructure Security Agency’s (CISA) Shields Up guidance, is well established advice and in line with recommendations in Trusted CI’s Framework and software assurance guidance. Trusted CI encourages members of the NSF community who are considering or are in the process of implementing controls such as those mentioned in the Fact Sheet to have discussions among their leadership team about accelerating deployment of those protections at this time.Trusted CI and OOI Complete Engagement
The Ocean Observatories Initiative (OOI, https://oceanobservatories.org/), funded by the NSF OCE Division of Ocean Sciences #1743430, is a science-driven ocean observing network that delivers real-time data from more than 800 instruments to address critical science questions regarding the world’s oceans. OOI data are freely available online to anyone with an Internet connection.
The OOI provides an exponential increase in the scope and timescale of observations of the world’s oceans. Present and future educators, scientists, and researchers are able to draw conclusions about climatological and environmental processes based on these measurements, requiring the data to be accurate, with a flawless pedigree. As a result, the OOI has a requirement to protect its data from being altered by any external agent.
To this end, OOI-CI (OOI Cyberinfrastructure) solicited a consultation from Trusted CI to evaluate their current security program, along with guidance on reviewing and evaluating potential alternatives for an enhanced security posture. We refined and prioritized OOI’s needs to the following goals: (i) perform a security review of OOI’s cyberinfrastructure using the Trusted CI Security Program Evaluation worksheet, (ii) take steps toward adopting the Trusted CI Framework by developing a “master information security policies and procedures” document (MISPP), (iii) investigate and document missing policies and procedures, including questions and concerns raised by OOI, and unknowns discovered in above exercises, and (iv) provide guidance on creating an asset inventory, applying a control set, and creating and maintaining a risk registry.
The OOI team completed the Trusted CI Security Program Evaluation spreadsheet. This exercise started the OOI team thinking about and discussing cybersecurity concerns that were raised in the evaluation, both in previously known topics, but also unknown or undefined areas. The Trusted CI team created a list of prioritized recommendations aligned with Framework Musts -- core concepts that every cybersecurity program should have -- that the OOI team can use in addressing or documenting gaps.
We introduced OOI to the Framework and Implementation Guide, and had discussions concerning the Musts, what they entail, and how they apply to and define a mature security program. The OOI team attended the 2021 NSF Cybersecurity Summit and specifically The Framework Workshop, where they were able to benefit from a deeper dive into the Framework and implementation guidance.
OOI displayed a solid grasp of the suggested security program solution, the Trusted CI Framework, and of what needs to be done to adopt it. Completely adopting the Framework was beyond the scope of this engagement, however OOI focused on (i) developing the top-level Master Information Security Policy & Procedures (MISPP) document, (ii) develop a Cybersecurity Strategic Plan, and (iii) develop supplemental security program policies, e.g., Incident Response Plan, Disaster Recovery, and Acceptable Use Policies.
In addition to creating top level policy documents, Trusted CI stressed the importance of having an up to date asset inventory as well as selecting and applying a base-line control set. The OOI team began identifying their critical assets as well as selecting CIS v8 as a control set and then aimed to apply controls from Implementation Groups 1 and 2. Trusted CI staff also provided a list of ‘high priority’ controls to focus on that would provide the best ROI for time and resources spent implementing.
We are pleased to announce that OOI is a participant in Trusted CI’s Framework Cohort taking place the first half of 2022 (1H2022). This will allow them to continue their work on creating and refining a mature security program while working with other NSF Major Facilities under the guidance and expertise of Trusted CI’s Framework team.
The engagement ran from August 16, 2021 to December 31, 2021, and was recorded in the document “OOI / Trusted CI Engagement Final Report” (https://hdl.handle.net/2022/27253).
Friday, March 11, 2022
Join Us at EDUCAUSE CPP Conference - Early Registration Ends 3/22
Training: Security Log Analysis
Tuesday, May 03 | 8:30AM–12:00PM ET
Presenters: Ishan and Mark
The security log analysis workshop walks participants through the security log analysis life cycle, providing considerations for centralized log collection and log management tools, phases of compromise, and examples from real attacks. We will be analyzing logs from Zeek Network Security Monitor, the Apache web server, two-factor authentication systems, cloud service logs, and others. This workshop also includes a hands-on exercise that will demonstrate techniques to analyze logs to detect security incidents using both the command line and Elastic Stack (aka ELK). The hands-on exercise will provide an overview of investigation techniques to determine security incident logs of some common attacks like SQL injection, filesystem traversal, brute force attacks, command-line injection, and more. Recent security vulnerabilities, such as log4shell, will also be discussed, along with techniques for detection. This will be an interactive session allowing Q&A and will also feature interactive polls to enhance participants' learning experience.
Training: Security in the Shell (or, How I Learned to Think Before Forking)
Tuesday, May 03 | 1:00PM–4:30PM ET
Presenters: Ishan and Mark
Although it is one of the oldest technologies in IT, the command line and terminal emulators continue to be in wide use for modern IT needs. Although people may think of these technologies as having a solid security footing, there are a number of ways someone can shoot themselves in the foot while using them, and I'm not just talking about running "rm -fr /". In this workshop, Mark Krenz, the creator of the popular Twitter account climagic, will demonstrate these and guide students through how to practice better command line security, from understanding the metadata that is generated by your favorite editor to knowing how to exploit SSH, knowing how to protect yourself when checking malware, and much more. There is something for everyone in this workshop, and you are sure to come away with a plethora of job-saving tips.
Breakout session: Security Recommendations for Science DMZs
Wednesday, May 04 | 10:45AM–11:30AM ET
Presenters: Ishan, Kathy, and Mark
A Science DMZ is a special network architecture designed to improve the speed at which large science data transfers can be made. They have become a common solution to the issue of busy academic networks causing slowdowns or failures of large data transfers. A new paper published by Trusted CI on the security of Science DMZs provides an overview of this type of network architecture, summarizing the current best practice cybersecurity risk mitigations as well as providing additional security recommendations. This session is a brief introduction to the Science DMZ concept and presents an overview of the mitigations documented in the paper.
Wednesday, March 9, 2022
Trusted CI Applauds JASON Report on Facilities Cybersecurity
In 2021, the NSF "commissioned a study by the JASON advisory group to assess and make recommendations regarding cybersecurity at NSF’s major facilities.” In December, NSF publicly released the seven recommendations from the JASON group and NSF’s response to those recommendations. Given Trusted CI’s role over the past 10 years in providing leadership and guidance to NSF Major Facilities, we welcomed the opportunity to contribute to the JASON group’s study and the dialogue it spurred. The following text consists of each of the JASON group’s recommendations, followed by the response from NSF, and Trusted CI’s response, which is the unique contribution of this document. We provide our responses to help the community understand how Trusted CI can help them as they consider these recommendations and their impact within their own projects.
- JASON recommendation: “NSF should maintain its current approach of supporting major facilities to enhance cybersecurity through assessments of risk, and development and implementation of mitigation plans. A prescriptive approach to cybersecurity should be avoided because it would be a poor fit to the diversity of facilities, would inefficiently use resources, and would not evolve quickly enough to keep up with changing threats.” NSF response: “NSF intends to maintain its current philosophy of performing oversight of awardee plans that are tailored to the unique natures of the individual major facilities. Through its review processes, NSF will ensure that these plans are consistent with best practices for cybersecurity that are in common between major research facilities and other types of infrastructure.”
2. JASON recommendation: “An executive position for cybersecurity strategy and coordination for major facilities should be created at NSF. This executive should have authorities that allow them to continually support the balancing of cybersecurity, scientific progress, and cost in the distinct ways that will be appropriate for each facility.”
NSF response: “NSF notes and agrees with the emphasis on such a position on strategy and coordination. NSF will explore different options for initiating the position and plans to create such a position within the next six months."
Trusted CI response: We strongly endorse this foundational recommendation and we look forward to collaborating with the new executive to fulfill our aligned missions. In Trusted CI’s experience, cybersecurity frequently proves ineffective or counterproductive when cybersecurity leadership lacks an understanding of the organization’s mission. An executive at NSF with expertise in both cybersecurity and the research mission would bring valuable additional perspective and leadership to NSF.
3. JASON recommendation: “Using annual reporting and review processes, NSF should ensure major facilities implement robust cybersecurity programs that remain consistent with current best practice.”
NSF response: “NSF plans to review the elements of a good facility cybersecurity program, currently described in Section 6.3 of the NSF Major Facilities Guide, to ensure that this section is up to date. NSF will add cybersecurity as a required element of annual reports and program plans and conduct any additional specialized reviews based on perceived risk.”
Trusted CI response: Trusted CI helps facilities develop cybersecurity programs that help ensure productive, trustworthy science. The Trusted CI Framework is a tool to help organizations establish and refine their cybersecurity programs. In March 2021, we released the Framework Implementation Guide for Research Cyberinfrastructure Operators, which contains detailed guidance that can help major facilities implement effective cybersecurity programs and thereby addresses Section 6.3 of the Research Infrastructure Guide.
4. JASON recommendation: “NSF should develop a procedure for response to major cybersecurity incidents at its major research facilities, encompassing public relations, coordination mechanisms, and a pre-ordained chain of authority for emergency decisions. Each major facility should also have their own response plan that is both specific to its needs and consistent with NSF's plan.”
NSF response: “NSF has charged a working group to develop a more robust response plan that integrates with both the agency's overall crisis communications plan and the response plans at the individual major facilities.”
Trusted CI response: Through our ongoing engagement activities with NSF Major Facilities and our mission "to lead in the development of an NSF Cybersecurity Ecosystem," we are uniquely positioned to provide guidance to this working group. During the past decade, we have built our understanding of cybersecurity challenges faced by the Major Facilities by hosting the annual Cybersecurity Summit, establishing and facilitating monthly meetings of the Large Facilities Security Team, and conducting 13 direct one-on-one engagements with the 10 of the Major Facilities. We look forward to bringing that experience, along with our ever-increasing understanding of the threat landscape faced by research facilities, to a productive collaboration with the working group and the executive identified in recommendation #2.
5. JASON recommendation: “NSF and the major facilities must be adequately resourced for their cyberinfrastructure and cybersecurity needs. What is appropriate will depend on each facility's unique characteristics and specific needs. The cybersecurity budget should be commensurate with perceived risk of an event, which may be unrelated to the cost of constructing or operating the facility.”
NSF response: “NSF will work with each awardee to develop a cybersecurity risk register for each major facility and will then integrate those risk registers in order to determine the highest NSF risks and implement any needed mitigations.”
Trusted CI response: We agree with the JASON group’s assertion that Major Facilities must be adequately resourced for their cybersecurity needs. Cybersecurity spending is a necessary focus area in the expanding dialogue among Major Facilities, NSF, and other relevant stakeholders. Adequate resourcing to address unacceptable cybersecurity risk is precisely the subject of the Trusted CI Framework’s Must 11. Cybersecurity risk registers may be a helpful tool assessing whether cybersecurity spending is commensurate with the threats posed by unmitigated risk. However, the need for the allocation of cybersecurity resources is fundamental.
6. JASON recommendation: “NSF should refine facility proposal and design review processes to ensure that new major facilities plan cybersecurity as an integral part of the information technology infrastructure. NSF should regularly review the cybersecurity plans and efforts of both new and existing major facilities. Shifts to cloud-based cyberinfrastructure and to a wider range of partners will impact cybersecurity planning and need to be considered at proposal time.”
NSF response: “NSF believes that the cybersecurity review process at the time of awards should be risk-based. NSF will work to ensure that cybersecurity is a specified element and review criterion of each call for proposals in a major facility competition. For a renewal proposal, NSF will include a requirement for submission of a cybersecurity plan. For a new construction award, or a project in the Design Stage, the cybersecurity plan will be required to be integrated with the Project Execution Plan. NSF will assure that appropriate expertise is present on review panels to assess the adequacy of the cybersecurity plan.”
Trusted CI response: We support the recommendation to require cybersecurity planning as part of facility proposal and design and would extend that recommendation to include the construction phase as well. For renewal proposals, we recommend expanding the requirement such that facilities must submit evidence of an active cybersecurity program (not just a plan). Trusted CI’s guidance provides facilities with the means to both plan and assess their programs. Prioritized, mission-based cybersecurity planning is central to the Trusted CI Framework, and we have demonstrated experience supporting NSF Major Facilities with cybersecurity strategic planning, through activities like the LFST, regular engagements, the NSF Summit and our 2022 Framework cohort.
7. JASON recommendation: “NSF should remain aware of national security concerns regarding its facilities and continue to facilitate coordination with appropriate agencies.”
NSF response: “NSF will conduct an assessment of national security concerns that may be associated with its major research facilities.”
Trusted CI response: Several members of the Trusted CI team have experience working at the intersection of cybersecurity and national security, and we are happy to be a resource to facilities in this area. Trusted CI has a long and successful history providing tailored, actionable guidance and expertise to NSF Major Facilities. The JASON working group’s recommendations are a strong endorsement of NSF’s direction, Trusted CI’s contribution, and if followed, represent a step forward in ensuring the security of our nation’s science. Collaborating with NSF and Major Facilities to enable trustworthy science is central to Trusted CI’s mission.