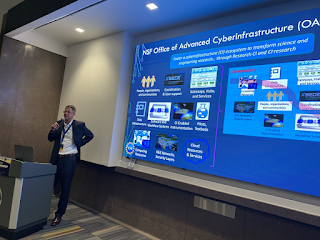
In October we hosted our
annual NSF Cybersecurity Summit. This year’s Summit was a hybrid event hosted at the Monroe Convention Center in Bloomington, IN. It was our first Summit with a face-to-face component since 2019. Our student program welcomed ten students to attend the in-person training sessions, network with fellow attendees, and introduce themselves to our community. We also matched students with mentors to help facilitate networking opportunities.
We give special thanks to our mentors: Ishan Abhinit, Fatema Bannat Wala, Mark Krenz, and Jim Marsteller.
We asked the students to share their thoughts on their experiences at the Summit. Below is a selection of their responses. These statements have been lightly edited for clarity.
Jacob Abbott, Indiana University, PhD in Informatics
While at the 2022 NSF Cybersecurity Summit I attended the “Regulatory Compliance for Research,” and “Physical Security,” workshops that gave substantial information before the plenary sessions started. During the course of the event, I was able to meet Doug Ertz from UNAVCO and we realized that we have a mutual acquaintance in industry and we both have mentored students in partnership with the Center of Excellence for Women & Technology. Hearing discussions from professionals in different research areas and backgrounds, such as one presentation about all the facilities and requirements for high powered magnetic field generators, was very interesting and just shows how ubiquitous the issues of cybersecurity are for everyone.
Jessy Ayala, UC Irvine, PhD in Software engineering
At the 2022 NSF Cybersecurity Summit, I had the pleasure of networking with student peers from different universities, professors, and cybersecurity professionals. It was a great opportunity to have fruitful conversations with those who tackle security problems from a different perspective and overall learn about relevant issues we face today because of emerging, and pre-existing, technologies. I'm glad I can keep in touch with some of the people I met and look forward to any collaborations that may arise.
Tria Correll, Middle Georgia State U, Bachelor's in Information Technology
Besides the knowledge I gained from the pre-conference training, the biggest takeaway from attending the 2022 NSF Cybersecurity Summit was the opportunity to connect with fellow cybersecurity students and professionals. I learned a great deal about the importance of physical security and gained insight into why there are security risks when using a command line interface. I hope I'm able to attend next year's Summit in Berkeley, CA.
Xinyao Ma, Indiana University Bloomington, PhD in Security Informatics/Data Science
My research interests focus on usable security, and how to help people safely use the Internet from a user's angle. It was my first time attending such a great Summit and having the chance to meet so many people who are also working and researching in the cybersecurity field. I attended two very useful workshops, got to know many people that I haven't had a chance to meet, and learned a lot about what other cybersecurity people are doing. I'm a Ph.D. student in the usable security area, and most times, I have to work and study alone. Most connections come from my school and the lab. The Summit gave me a chance to get to know many other students and professors who also work in this area, and especially thanks to my mentor James Marsteller, who was really nice when I was afraid because I didn't know anyone before.
Rajvardhan Oak, UC Davis, PhD in Computer Science
The 2022 NSF Cybersecurity Summit was a great learning experience for me. It was an opportunity to learn cyber security skills through theory as well as hands-on exercises and keep up to speed with the latest in the field. It was also an excellent forum to network with industry professionals, fellow students and faculty. This has resulted in a fruitful collaboration for me; I am currently in touch with a fellow student and in the process of designing a research project in cyber security. I’m very fortunate that I was able to attend the Summit!
Harsh Parekh, Louisiana State University, PhD in Information Systems
2022 NSF Cybersecurity Summit's student program had an eclectic mix of students from diverse academic backgrounds. The Summit gave me immense networking opportunities with interdisciplinary researchers and practitioners in the cybersecurity space. I have already started some collaborative research projects through networking made possible through the Summit. Being a behavioral security researcher, I had a limited understanding of technical and developmental cybersecurity research which was rightly introduced through workshops such as log analysis and machine learning in cybersecurity. The student program was well planned with designated mentors, Summit events, social nights, and a tour of IU's massive data center. I really enjoyed my time in Bloomington and would like to be associated with the Summit in the future.
Mahmoud Shabana, NYU Tandon School of Engineering, MS Cybersecurity
 The NSF Cybersecurity Summit was a great experience as my first in-person cybersecurity conference! I was fortunate to learn about how machine learning can be pivotal in implementing cyber defense tools, as well as new security techniques in log analysis. Outside of workshops, I got to meet professionals in all fields of security research and development. Connecting with current security researchers and practitioners has helped expand my network in security and learn from leading experts from around the world!
The NSF Cybersecurity Summit was a great experience as my first in-person cybersecurity conference! I was fortunate to learn about how machine learning can be pivotal in implementing cyber defense tools, as well as new security techniques in log analysis. Outside of workshops, I got to meet professionals in all fields of security research and development. Connecting with current security researchers and practitioners has helped expand my network in security and learn from leading experts from around the world!
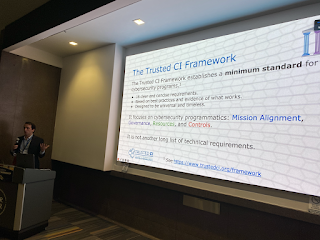
Joshua Thornburgh, University of Arkansas, MS in Computer Science
This Summit was the first of its kind for me to attend. Coming into it, I wasn’t sure what to expect or what the Trusted CI Framework was really about, not to mention a bit of imposter syndrome for even being invited. That was quickly dissolved once I began speaking with people. Everyone was extremely nice and had loads of wisdom to share. Having sat through the workshops for both machine learning in cybersecurity and the overview of the Framework, I can say with confidence that what I gained will really aid in my future paths. While the Trusted CI Framework is currently not something I can utilize as a student, that I have seen yet, I will carry it with me for when I do need it. Coming to the 2022 NSF Cybersecurity Summit was a true honor and I look forward to participating in this community in the future.
Alexs Wijoyo, Pace University, MS in Cybersecurity
The NSF Summit brought much clarity to the impact of cybersecurity at every scale no matter what industry you are in. Interacting with many of the individuals that were in charge of implementing the TrustedCI Framework and the mentors, I learned that there's always a place for security even at the lowest level. I learned many skills in the pre-conference workshops regarding command line security and log analysis with the use of ELK Stack as well as making many memories with the peers that I was able to spend my time with. My best moment is touring the University of Indiana data center and looking at the infrastructure that the school has built to support the endeavors of the staff and their students.
Alenna Zweiback, Indiana University, Bachelor's in Information Systems and Cybersecurity
I had an incredibly influential experience at the 2022 NSF Cybersecurity Summit. Prior to the conference, I was interested in learning more about how I can further my skills and career development in cybersecurity. By attending this conference, I was able to meet a variety of like-minded students, professors, researchers, consultants, and many other unique individuals. I became mindful of new internship opportunities. I envisioned long-term career paths. Throughout the conference, I absorbed just how necessary it is for more people to be aware and involved in cybersecurity. My biggest takeaway from this conference was from keynote speaker, Helen Patton. When discussing the evolution of cybersecurity she quoted Mikko Hyppon in saying, “We are no longer securing just computers - we are securing the society.” By attending this conference, I was able to take one more step in educating society.
We are so proud of our student attendees and look forward to what they do in the future.